Secure browser-based access to your servers using Apache Guacamole
Leverage CSE's ability to secure hosted websites and its capability as a federated IDP to manage access to desktop environments via Guacamole.
Overview
Apache Guacamole is an open source client-less remote desktop gateway. Guacamole allows your end-users to use their browsers to access desktop environments; under the hood, Guacamole uses remote desktop protocols (such as VNC or RDP) to set up the connection.
You can leverage CSE’s ability to secure Hosted Websites, combined with its capability as a Federated Identity provider, to manage access to desktop environments via Guacamole. Your end-users will be able to access their desktop environment conveniently via the browser, without needing VPN access. Best of all, you can enforce Zero Trust access policies as you would for any hosted web service.
Guacamole Configuration
This article assumes you have good familiarity with the Guacamole Manual and have a working installation of the Guacamole server that is configured for SAML.
If you don’t already have a working Guacamole installation, you can follow CSE’s setup guides to:
- Deploy Guacamole Proxy and MySQL - use Docker containers and initialize the database
- Configure Guacamole for SAML Authentication - install the SAML extension and IDP settings
- Set up the Primary Admin - configure the DB for a primary admin for Guacamole
Prerequisites
- Created the application integration called “CSE TrustProvider” following our instructions to set up an IdP as your Identity Provider.
- Installed a CSE Access Tier in the same network segment as the server to be exposed using CSE.
- Installed the latest CSE App on your desktop machine, and registered with a valid organization.
Setup
Step 1. Create a Policy
1.1 Log in to the CSE Command Center and navigate to Secure Access > Policies > Create New Policy.
1.2 Create a new Policy using the template Basic Authorization Policy for Users.
1.3 Enter a Policy Name (such as, hosted-service) and a Description.
1.4 Configure the Policy Attributes for minimal controls:
- Specify this policy is intended for Web - for accessing HTTP services via web browser
- Only allow access from the following role: ANY
- Only allow users and devices with the following Trust Levels: No Trust Level - ignore TrustScore (or a Trust Level according to your organization’s security requirements)
Step 2. Register Guacamole as a Hosted Web Service (for VPN-Free Access)
2.1 Navigate to Manage Services > Hosted Services and then click + Register Service.
2.2 Select the template Standard Website.
2.3 Enter the Service Name (such as, Guacamole Web) and Description (such as Access to hosted Guacamole server).
2.4 Click Select an Icon, then search for and select an icon.
2.5 Select the cluster where the applicable Access Tier is located.
2.6 Configure the Service Attributes:
- Enter the Service Domain Name of the Access Tier behind which Guacamole proxy is deployed (such as,
guac.corp.example.com) and leave the port as443. - Set the enforcement model to Site-based (Access Tier) and then select the applicable Site (Access Tier).
- Enter the Backend Domain Name and Port.
- Enable TLS if Access Tier will be communicating to the backend web service using TLS.
2.7 Attach the policy we had previously created in Step 1.4, and then set enforcement mode to Enforcing.
2.8 Click Register Service.
Step 3. Register Guacamole as a SaaS Application (for SAML Authentication)
3.1 Navigate to Manage Services > SaaS Applications and then click + Register App.
3.2 Enter the SaaS Application Name (such as, Guacamole SAML) and Description (such as SAML authentication for Guacamole).
3.3 Configure the Authentication Federation settings:
- Set Authentication Protocol to SAML
- Set the Redirect URL (SAML ACS) to: https://guac.corp.example.com/guacamole/api/ext/saml/callback (the format will the the Web Service Domain Name +
/guacamole/api/ext/saml/callback) - Set the Audience URI (Service Provider Entity ID) to: http://18.220.182.177:8080/guacamole (the format will be IP Address of the backend for the web service +
/guacamole) - Set the Name ID Format to: Email
- Set the NameID Value to: Legacy compatibility mode
3.4 You’ll also need to note the Metadata URL for use in configure the SAML authentication in the Guacamole server configs.
Step 4. Navigate to the Guacamole instance and log in
4.1 Now, you can navigate to your Guacamole instance at https://guac.corp.example.com.
You will be taken to your Identity Provider to login while, behind the scenes, CSE is evaluating device posture and enforcing your security policies.
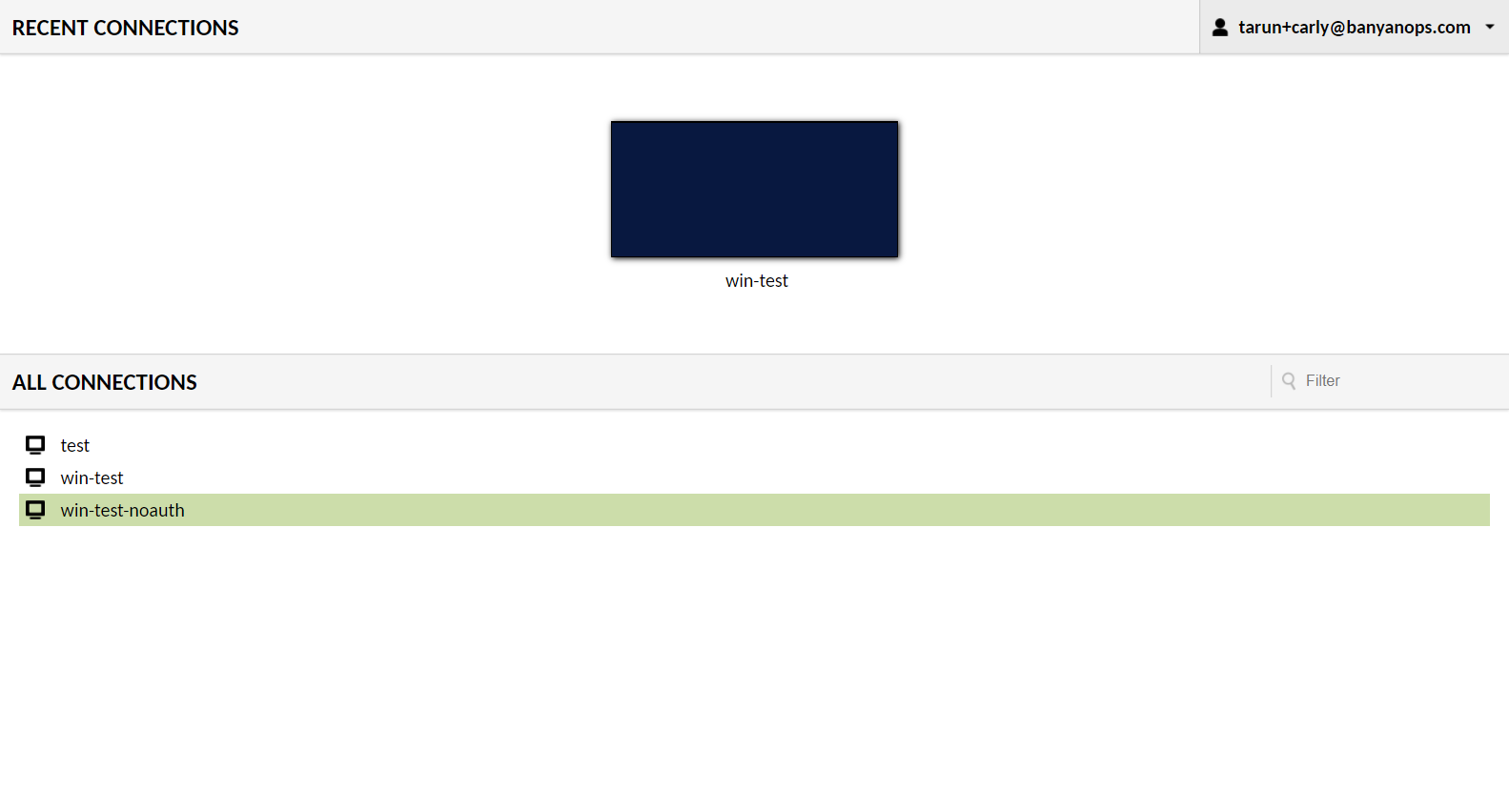
Once access in granted, you can use Guacamole’s native capabilities to configure and access desktop environments.