Securing Databases with SonicWall Cloud Secure Edge (CSE)
- Updated on
Overview
Access to infrastructure services (e.g., SSH/RDP Servers, Kubernetes, databases, and generic TCP services) is regularly needed by Operations and Engineering teams. Traditionally, access relied solely on generating long-lived passwords or long-lived SSH key-pairs per user. Long-lived credentials and keys can be a security risk, given the ease with which they can be shared or lost.
With Cloud Secure Edge (CSE), you add on a mandatory access control layer that continuously evaluates the security posture of the device and integrates with your org’s Single Sign-On (SSO) provider. All traffic to infrastructure services is transparently upgraded to Mutual-Auth TLS using short-lived X509 certificates. Security policies can then be continuously enforced, locking down access to specific servers based on user and device attributes and Trust Levels.
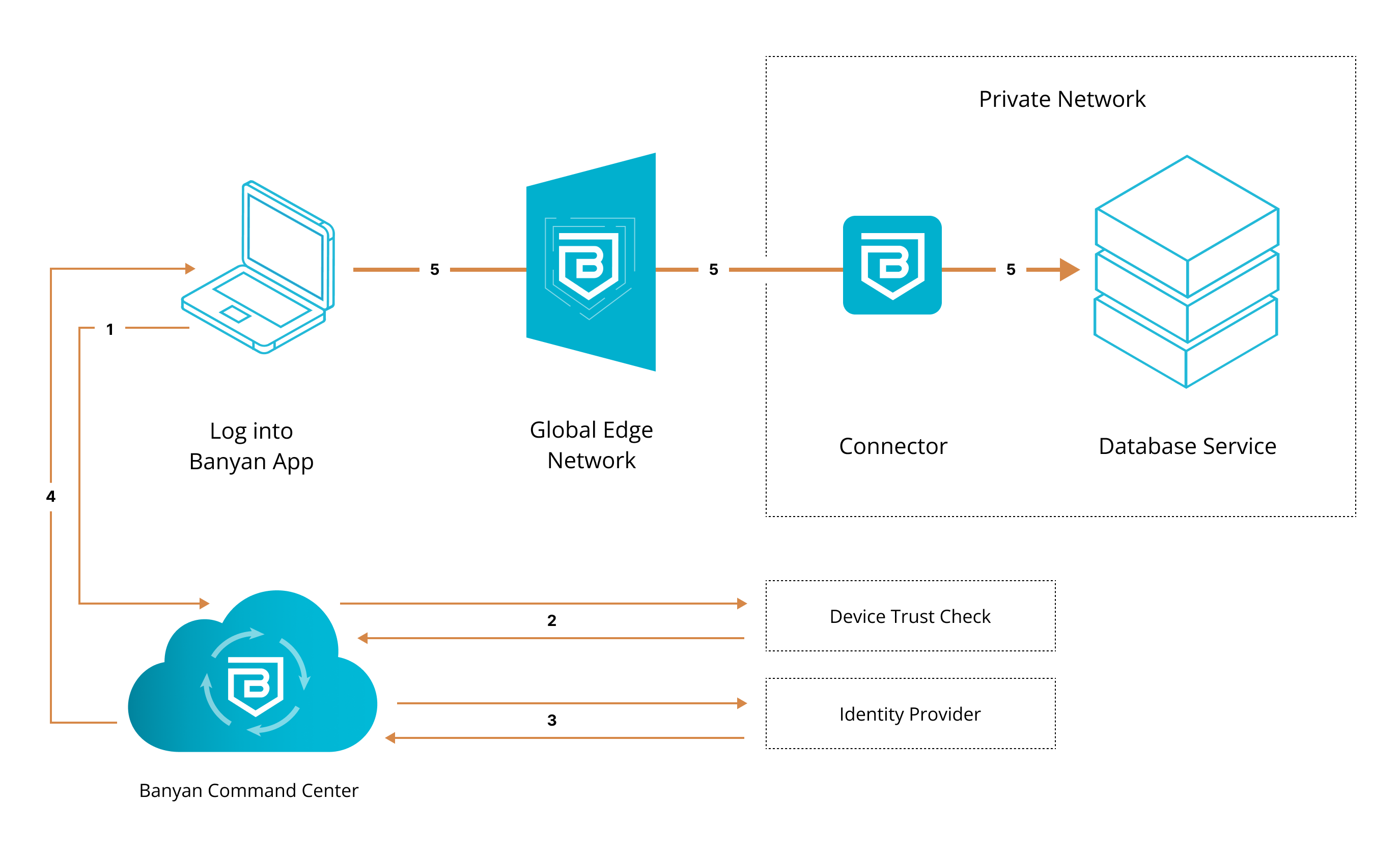
1. End user requests access to database service. User’s request is routed to CSE.
2. CSE runs a device trust check via user’s org’s device manager, which is integrated with the CSE app.
3. Once verified, the device is then authenticated via their org’s identity provider.
4. Once authenticated, user’s device is issued a Trust Cert. CSEproxy adds the Trust Cert to the user’s request.
5. User’s request is passed to the Global Edge Network, relayed to the Connector inside the org’s private network, and then sent to the database service.
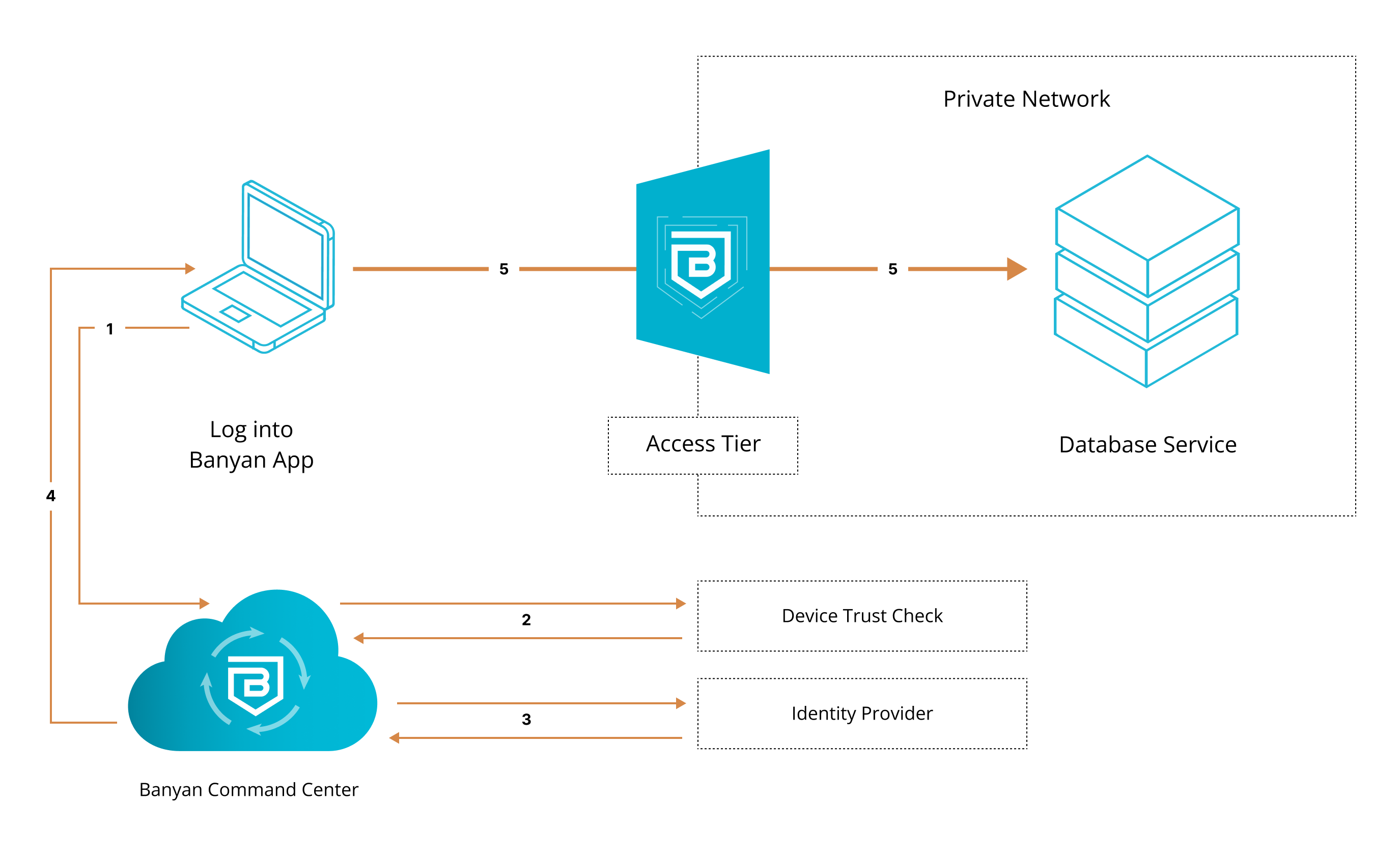
1. End user requests access to database service. User’s request is routed to CSE.
2. CSE runs a device trust check via user’s org’s device manager, which is integrated with the CSE app.
3. Once verified, the device is then authenticated via their org’s identity provider.
4. Once authenticated, user’s device is issued a Trust Cert. CSEproxy adds the Trust Cert to the user’s request.
5. User’s request is passed to the self-hosted Access Tier inside the org’s private network, and then sent to the database service.
Steps
Enable secure access to the database in three steps.
Step 1. Create a Policy
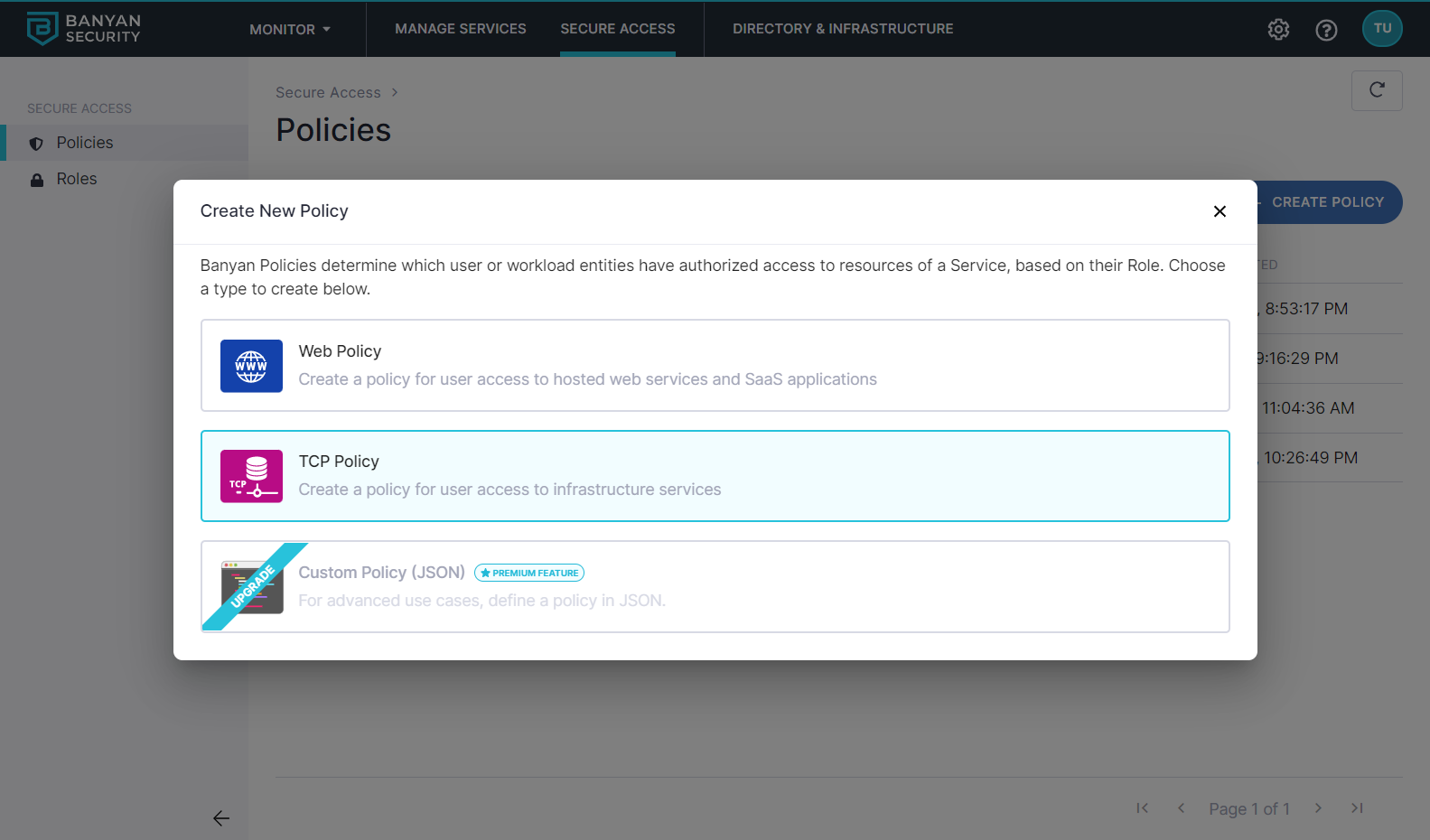
1.1 Log into the Command Center, and navigate from Private Access > Access Policies > + Create Policy.
1.2 Create a new policy using the Infrastructure Policy template.
1.3 Enter a Policy Name (such as, hosted-service) and a Description.
1.4 Configure the Policy Attributes:
- Only allow access from the following role: ANY (or a role according to your organization’s requirements)
- Only allow users and devices with the following Trust Levels: No Trust Level - ignore TrustScore (or a Trust Level according to your organization’s security requirements)
Step 2. Register database as a hosted service
2.1 Navigate from Private Access > Infrastructure, and then select + Register Service.
2.2 Select the Database Service template.
2.3 Enter the Service Name (e.g., AWS RDS) and Description (e.g., Access to hosted AWS RDS service).
2.4 Select the cluster where the applicable Access Tier is located.
2.5 Under Service Attributes, select an Access Tier.
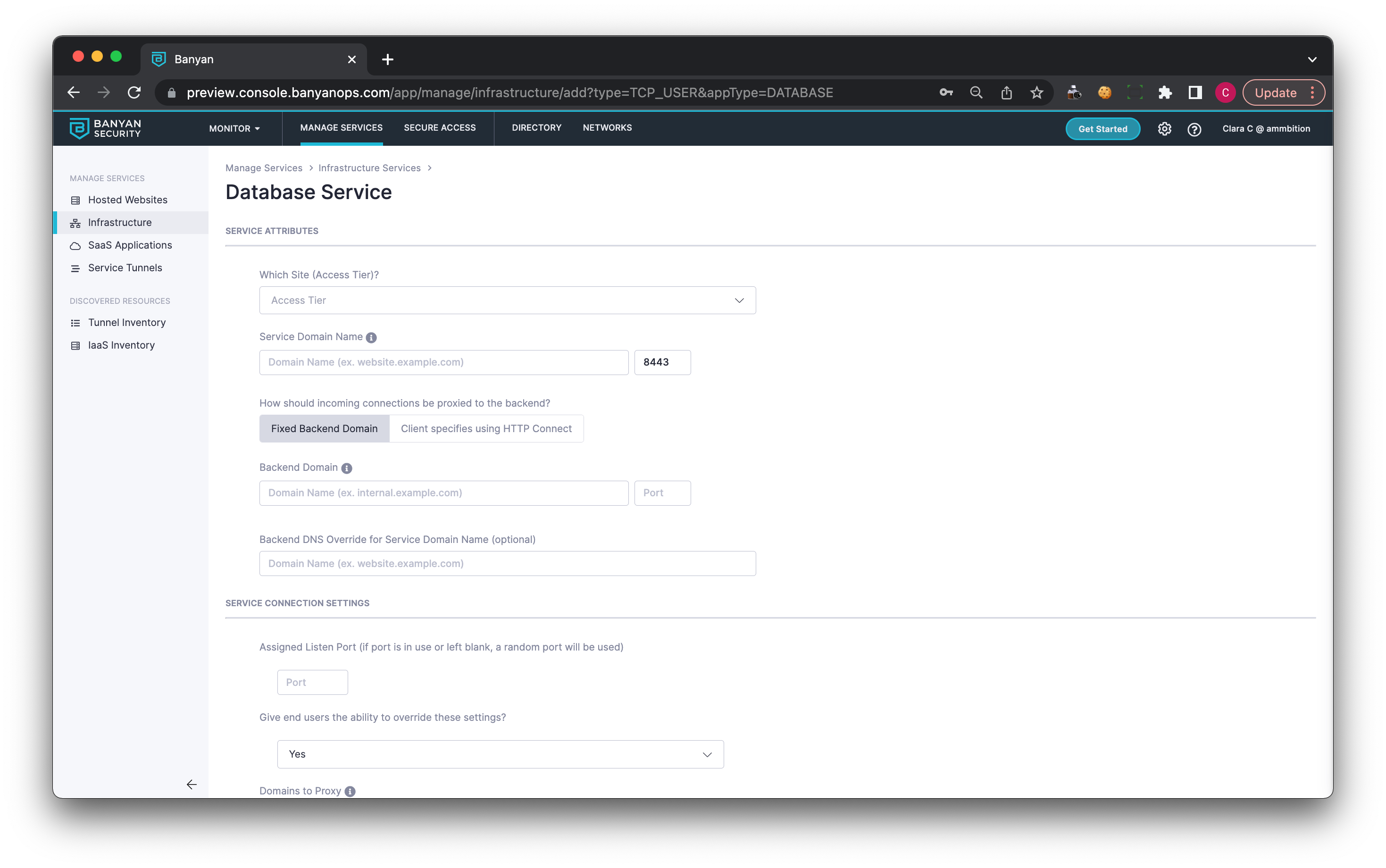
2.6 Enter the Service Domain Name of the Access Tier behind which the AWS RDS service is deployed, and leave the port as 8443.
2.7 Set the incoming connections to be proxied to the Fixed Backend Domain.
2.8 Enter the Backend Domain Name and Port.
2.9 Optional: Enter the Backend DNS Override for Service Domain Name.
2.10 Under Service Connection Settings:
- Optionally, set an Assigned Listen Port or leave it blank to use a random port
- Optionally, allow or deny end users the ability to override these settings in the desktop app
- Enter domains to proxy: If specified, banyanproxy will intercept requests to ONLY these domains and forward them to the Access Tier; all other requests will be sent directly to their intended destination.
2.11 Attach the policy you created in Step 1.4, and then set enforcement mode to Enforcing.
2.12 Select Register Service.
Step 3. As an end user, launch the desktop app and access the database
3.1 Launch the desktop app, locate the hosted database (e.g., Amazon RDS) server from the list of Infrastructure Services, and then select Connect.
3.2 Click into the service details and take note of the (localhost:port) provided in the desktop app (for example, 127.0.0.1:XXXXX).
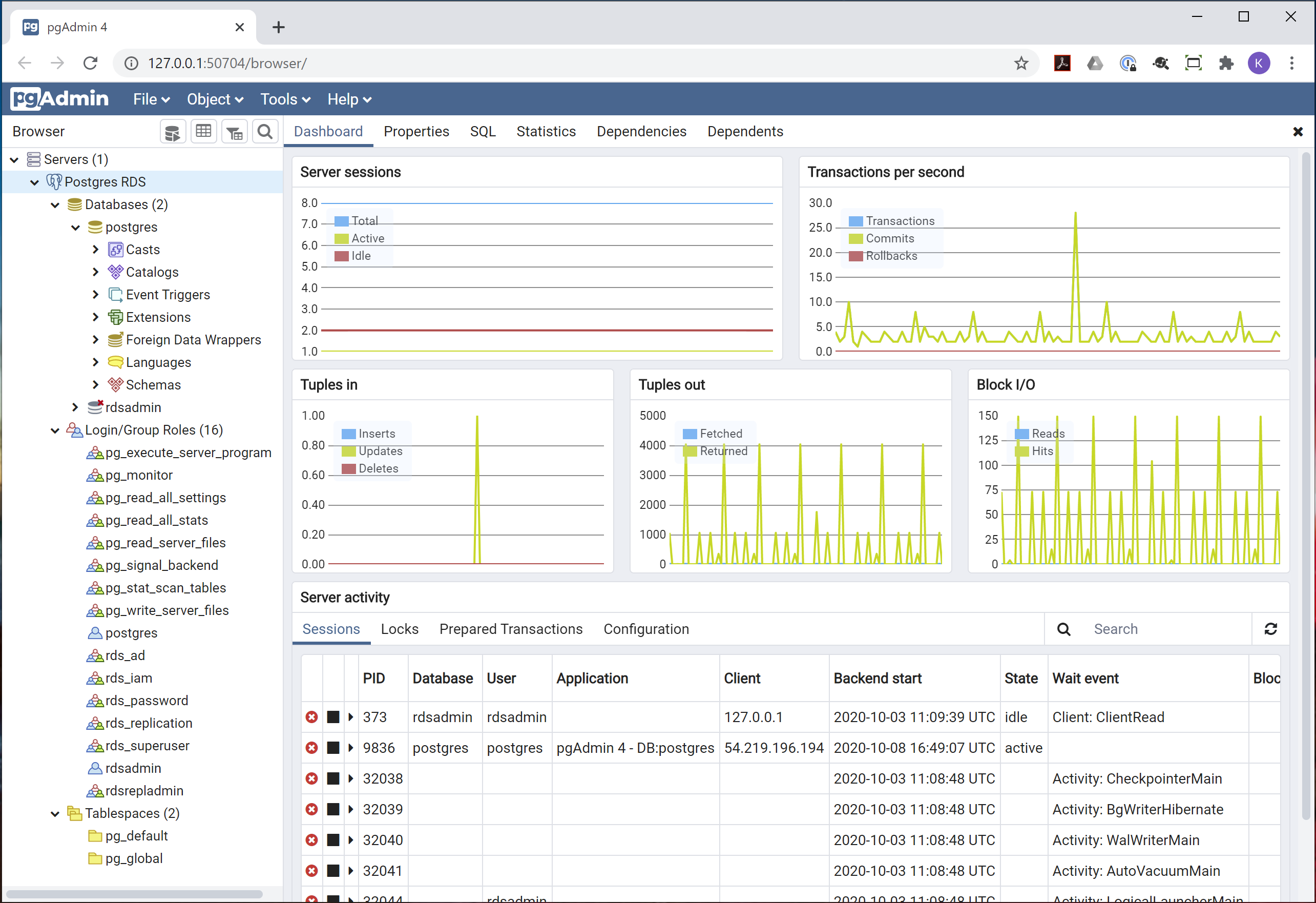
3.3 Launch your preferred database management tool (such as Microsoft SQL Server Management Studio, pgAdmin, phpMyAdmin, MySQL Workbench, etc.), and then create a new server using the localhost:port noted in the previous step. If necessary, enter your credentials to authenticate.
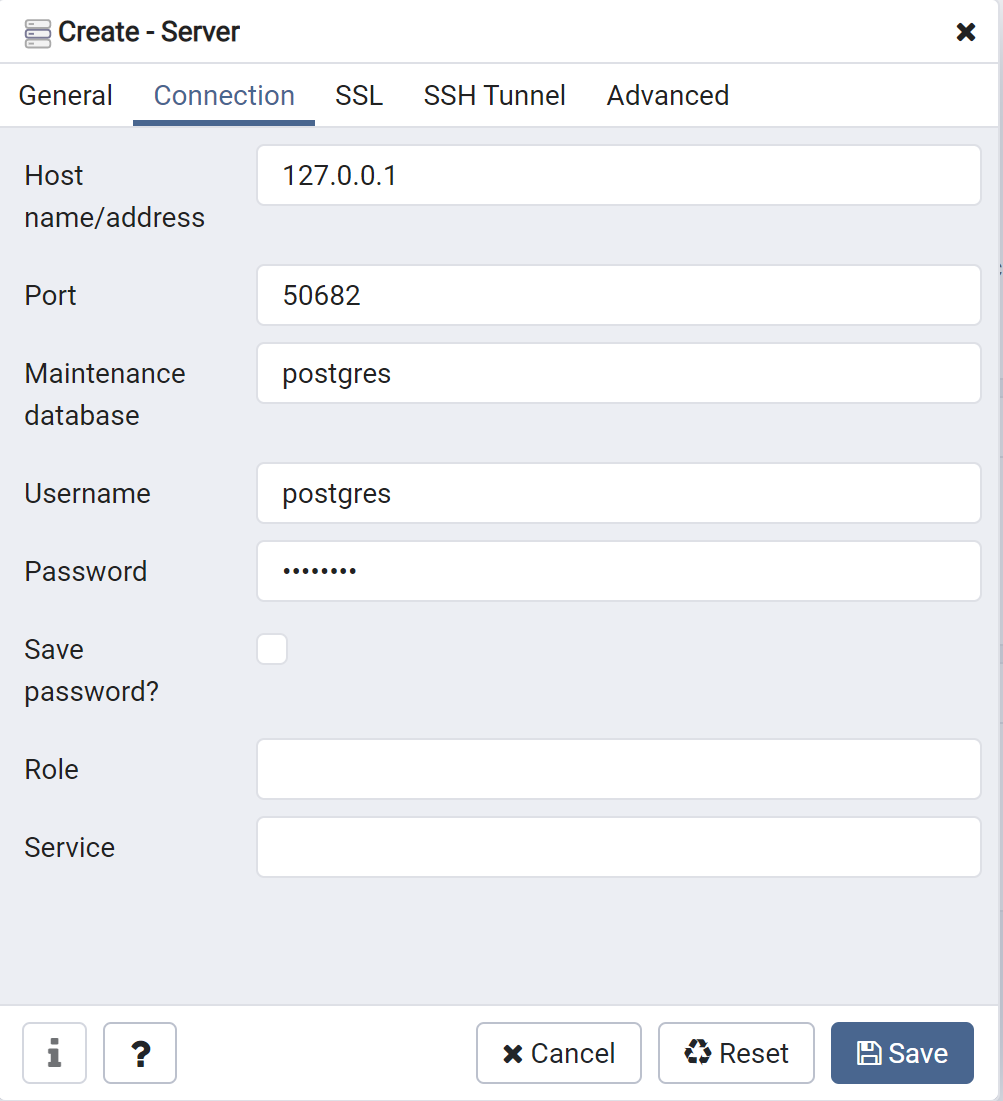
Behind the scenes, CSE evaluates your device posture, enforces your security policies, and grants access accordingly.