Enforce device trust for access to Dropbox
Configure Dropbox SAML authentication to use CSE's federated Identity Provider so you can enforce device posture requirements.
Overview
Dropbox is a file hosting service that offers cloud storage, file synchronization, personal cloud, and client software.
Prerequisites
In order to set up this integration, you need will need:
- A Dropbox Business Team on an Advanced or Enterprise plan.
- Administrative access to your Dropbox Team, with the ability to add an external SSO Provider.
- Dropbox’s post-back URL (such as
https://www.dropbox.com/saml_login, but ensure you are using Dropbox’s latest post-back URL).
We also assume you have already created the application integration called “CSE TrustProvider” following our instructions to set up an IdP as your Identity Provider.
Setup
Step 1. Create a Policy
1.1 Log in to the CSE Command Center and navigate to Secure Access > Policies > Create New Policy.
1.2 Create a new Policy using the template Basic Authorization Policy for Users.
1.3 Enter a Policy Name (such as,user-saas) and a Description.
1.4 Configure the policy attributes for minimal controls:
- Specify this policy is intended for
Web - for accessing HTTP services via web browser - Only allow access from the following role: ANY
- Only allow users and devices with the following Trust Levels: No Trust Level - ignore TrustScore (or a Trust Level according to your organization’s security requirements)
Step 2. Register Dropbox as a SaaS App
2.1 Navigate to Manage Services > SaaS Applications and then click + Register App.
2.2 Enter the SaaS Application Name (such as, Dropbox) and Description (such as Access to Dropbox).
2.3 Configure the Authentication Federation settings:
- Set Authentication Protocol to SAML
- Set the Redirect URL (SAML ACS) to the post-back URL provided by Dropbox (such as
https://www.dropbox.com/saml_login) Audience URI (Service Provider Entity ID) - Set the Audience URI (Service Provider Entity ID) to
Dropbox - Set the Name ID Format to Email
- Set the NameID Value according to your business needs.
- Use passthrough Name ID persists the NameID from your IdP
- Custom enables a NameID Custom Attribute field to enter an attribute supported by your IdP
2.4 Attach the policy created in Step 1 (above), and then set enforcement mode to Enforcing.
2.5 Click Register.
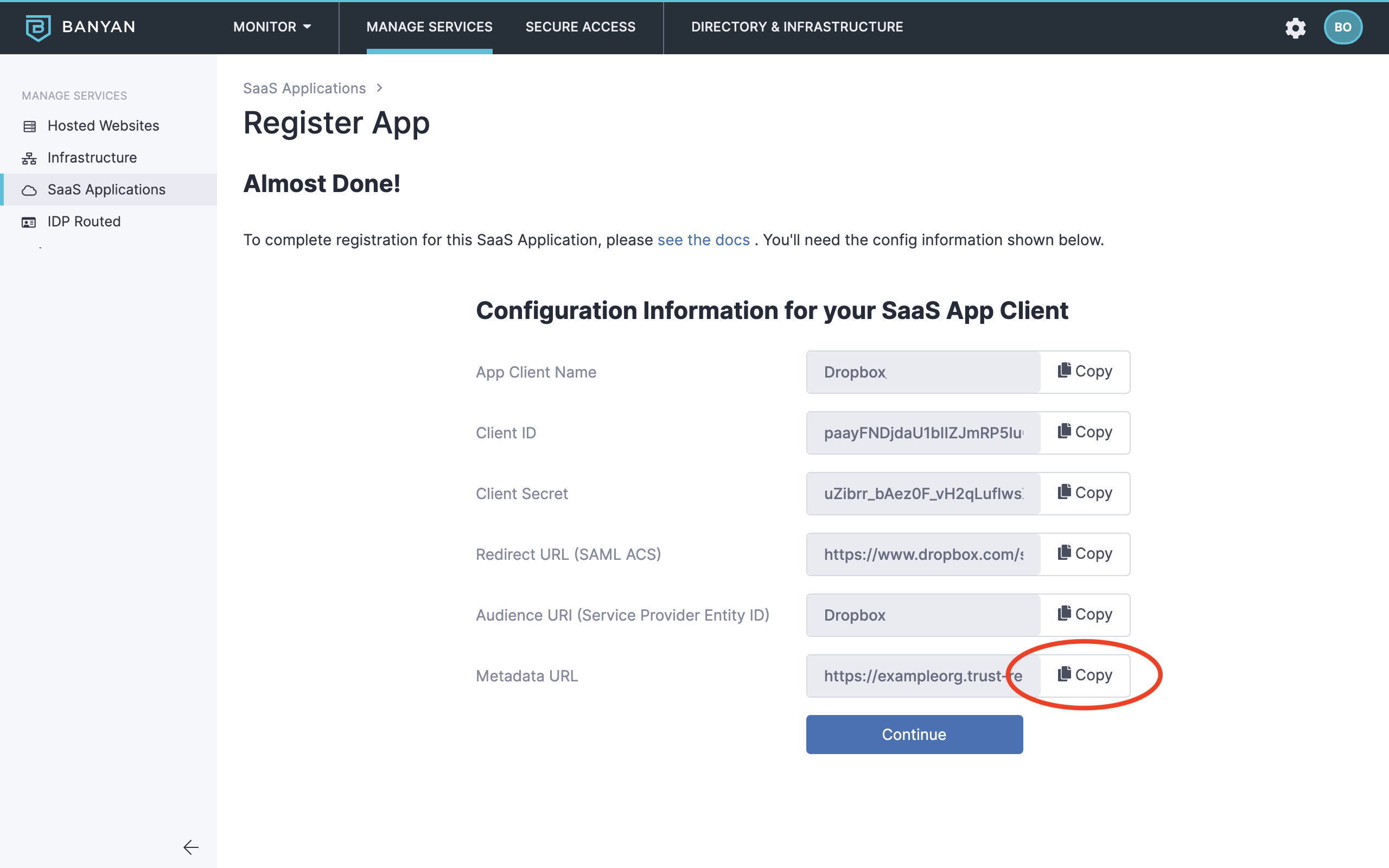
2.6 Copy the Metadata URL, paste it in your browser search bar and then press enter to download the xml file. You will use the information in this file to configure SSO in your Dropbox Team.
Step 3. Prepare your CSE-registered App Details for Dropbox
3.1 Open the metadata xml file downloaded in Step 2 (above) in your preferred text editor.
3.2 Locate and copy the X509Certificate string, and then paste it in a separate, new text editor file.
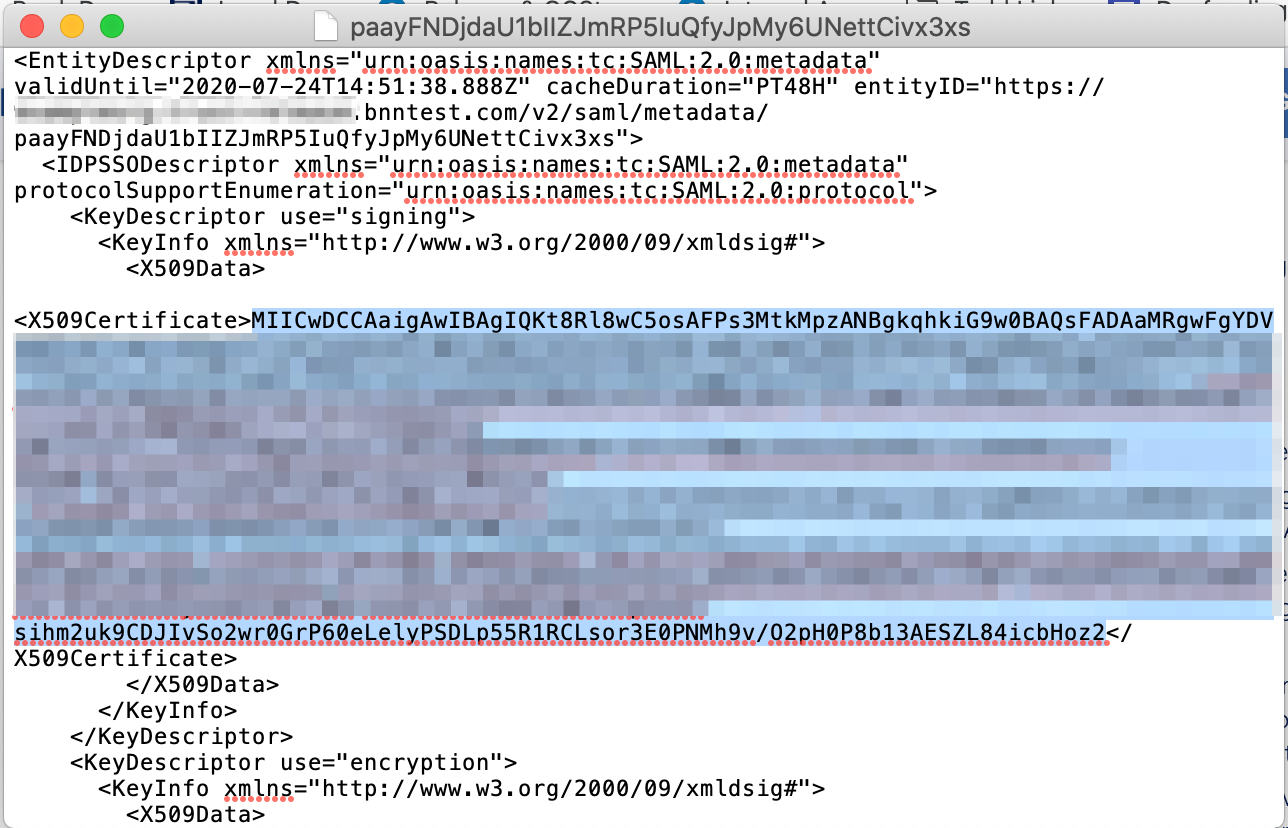
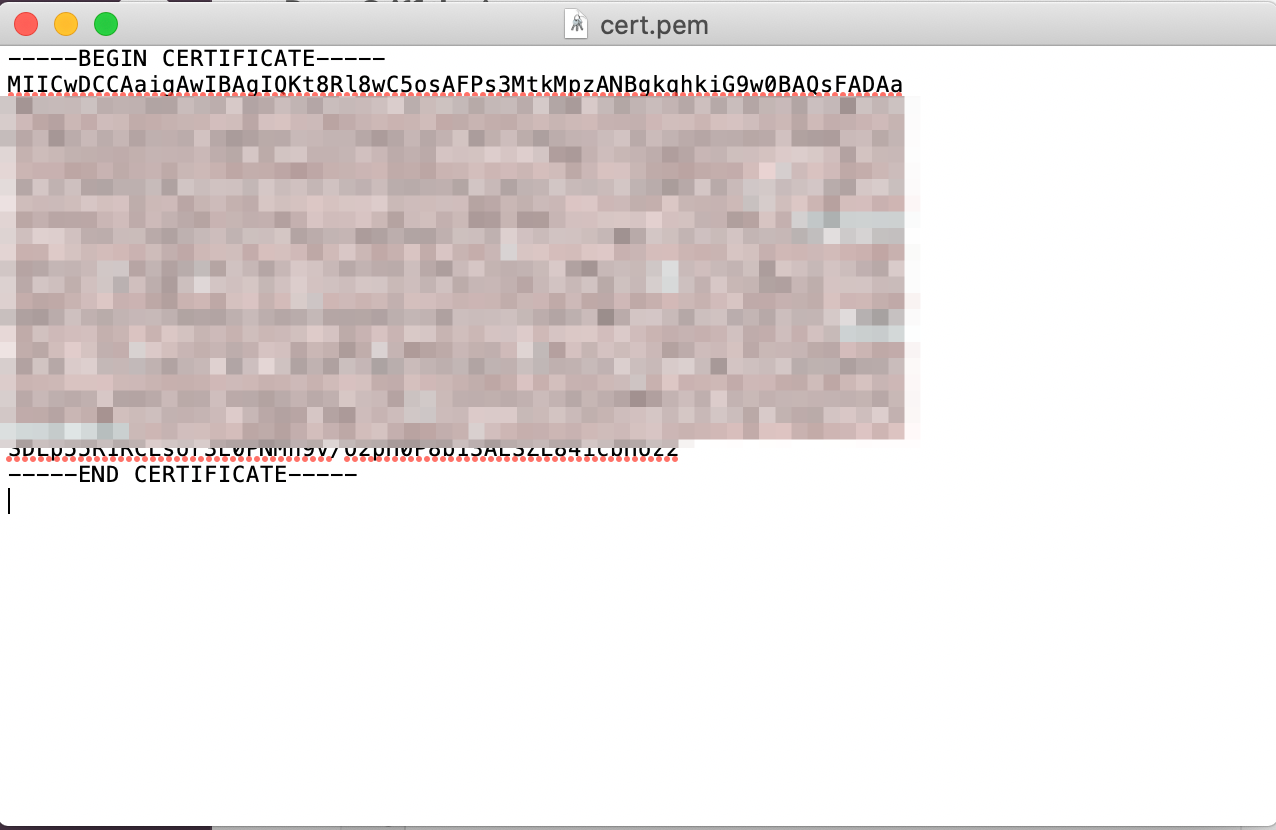
3.3 Format the string and then save it as a pem file. You will upload this file in Step 4 (below).
- Ensure you add the header (
-----BEGIN CERTIFICATE-----) to the first line. - Ensure you add the footer (
-----END CERTIFICATE-----) to the last line. - Ensure you add line breaks so that each line is no longer than 64 characters max.
- The formatted pem file should look like the example below:
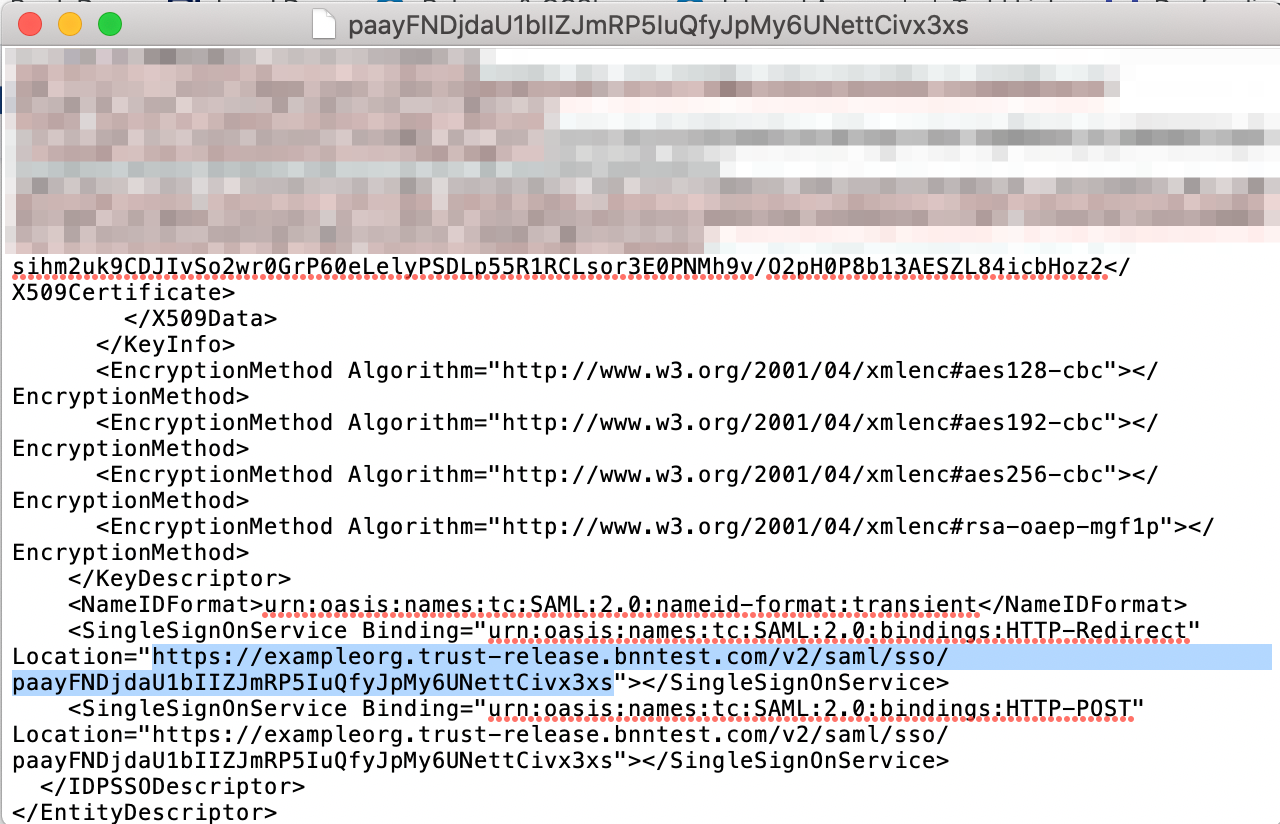
3.4 Also in the downloaded metadata xml file, locate and take note of the <SingleSignOnService Location> string. You will enter this value in Step 4 (below).
Step 4. Configure your Dropbox to use CSE for authentication
4.1 Log in to your Dropbox account, and then navigate to Admin Console > Settings > Authentication > Single sign-on.
4.2 Toggle the Single sign-on setting from Off to either Optional or Required, depending on your team’s needs.
4.3 Click Add sign-in URL, and then enter the <SingleSignOnService Location> string noted in Step 3.4 (above).
4.4 Click Upload certificate to upload the X.509 certificate pem file created in Step 3.3 (above).
4.5 Click Save.
4.6 Copy the SSO sign-in URL, which you’ll use in the step below.
Step 5. Navigate to Dropbox and login in via SAML
Now, you can navigate to Dropbox and authenticate using the SSO sign-in URL copied in the previous step.
You will be taken to your Identity Provider to login while, behind the scenes, CSE is evaluating device posture and enforcing your security policies.