Certificate Authentication for MySQL
Leverage SonicWall Cloud Secure Edge (CSE) short-lived x509 Certificates to manage end user access to MySQL servers, including access control and audit logging
- Updated on Jan 08, 2025
Overview
It’s often quite difficult to manage and share passwords and accounts between developers for database access. By leveraging CSE’s Mutually Authenticated TLS (MTLS) flows for TCP services, and combining that with Certificate-Based authentication using short-lived x509 certificates, it’s possible to provide your end users VPN-free zero-trust database access regardless of their network location.
Since the Cloud Secure Edge automatically provisions short-lived x509 certificates for your users when they log in, it natively provides the ability to authenticate and authorize users against MySQL Databases. This gives end users the ability to connect to MySQL Databases without a VPN, authenticate against the database directly through the Desktop App, and authorize users with native MySQL access control.
The CSE database access mechanism works seamlessly with the Mutually Authenticated TLS (MTLS) mechanism, letting you choose one or both capabilities based on your needs.
How It Works
With CSE, you modify your MySQL server to require client certificates signed by your CSE Root CA (formerly your Banyan Root CA), which can be obtained from the Command Center.
The MySQL Client connection flow using CSE login certificates leverage the in-build client-certificate authentication mechanism that MySQL provides, but also wraps the connection in an MTLS tunnel for complete VPN-free access.
Steps
Setting up VPN-free access to a MySQL Database is very similar to the setup process followed to secure a TCP service, as described in Notes on Securing TCP Services.
Then, there are a few additional steps to enable CSE Client Certificate Authentication:
- 1. In the Command Center, retrieve the CSE Root CA
- 2. Provision a Server Certificate using Let’s Encrypt
- 3. Modify MySQL for SSL and Client Certificate Authentication
- 4. Configure MySQL to require x509 Certificates issued by CSE
- 5. Connect to MySQL using the MySQL Client
1. Retrieve the CSE Root CA
We will use CSE’s ability to provision short-lived x509 certificates for end users (called login certificates) to authenticate with the MySQL Database.
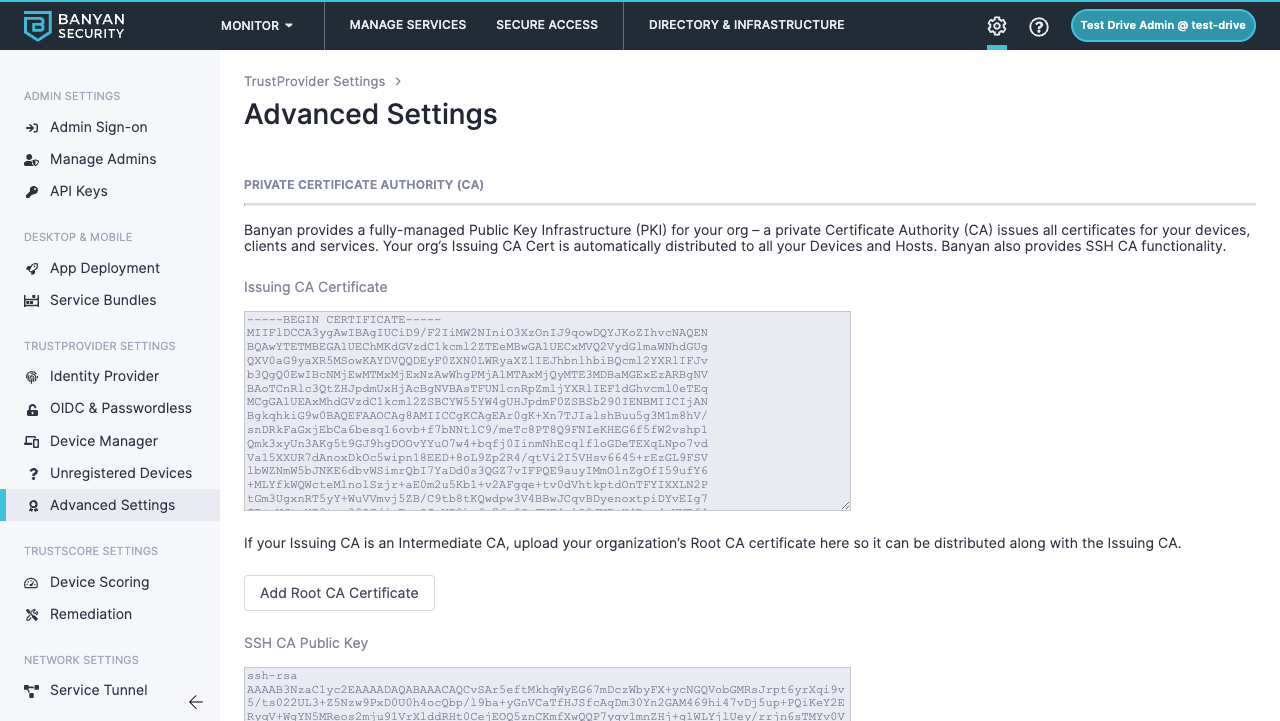
Navigate to Settings > TrustProvider Settings > Advanced Settings and copy the Issuing CA Certificate to your MySQL Server Host at /etc/ssl/certs/banyan-ca.crt. This will be used in later steps.
2. Provision a Server Certificate
In order for the MySQL Client to verify your server’s identity, you will need to obtain a server. You can use a self-signed private certificate (using OpenSSL or other such tool) or a public certificate here.
3. Modify MySQL for SSL and Client Certificate Authentication
At this point you should have the following certificates present on the MySQL Server Host:
/etc/ssl/certs/banyan-ca.crt/etc/ssl/certs/mysql-server.crt/etc/ssl/certs/mysql-server.key
And they should be owned by the mysql user on the host:
$ sudo chown mysql:mysql /etc/ssl/certs/banyan-ca.crt /etc/ssl/certs/mysql-server.crt /etc/ssl/certs/mysql-server.key
$ sudo chmod 0600 /etc/ssl/certs/mysql-server.key
Next, you’ll need to modify your MySQL configuration file, named my.cnf. This can often be found at /etc/mysql/my.cnf or /etc/my.cnf. You will need to configure this file to tell MySQL to require clients to connect over TLS and where to look for the Banyan CA:
#...
[mysqld]
ssl-cert=/etc/ssl/certs/mysql-server.crt
ssl-key=/etc/ssl/certs/mysql-server.key
ssl-ca=/etc/ssl/certs/banyan-ca.crt
require_secure_transport=ON # Used to require TLS for connections
#...
With this configured it may be required to restart your mysqld process. This can often be done by running sudo systemctl restart mysql.
4. Configure MySQL to require x509 Certificates issued by CSE
Next, we need to tell MySQL to use client-certificate authentication and ensure clients present a certificate from the CSE CA when they connect.
MySQL requires client certificates on a per-user basis. The requirement can be configured using CREATE USER or ALTER USER statements. When set, MySQL will reject connections from these users if they don’t present a valid certificate signed by your CA.
In this example we will be modifying the root user to grant access to any authenticated CSE User:
mysql> CREATE USER 'root'@'%' REQUIRE ISSUER '/O=YOUR_ORG_NAME/OU=Certificate Authority/CN=YOUR_ORG_NAME Banyan Private Root CA';
Where YOUR_ORG_NAME is the name of your Banyan Organization.
It is also possible to configure access for a single authenticated Banyan User:
mysql> CREATE USER 'root'@'%' REQUIRE ISSUER '/O=YOUR_ORG_NAME/OU=Certificate Authority/CN=YOUR_ORG_NAME Banyan Private Root CA' AND SUBJECT '/OU=Banyan Client USER_EMAIL/CN=Banyan Client USER_EMAIL';
Where YOUR_ORG_NAME is the name of your CSE Organization and USER_EMAIL is the email address of the registered Banyan User.
5. Connect to MySQL using the MySQL Client
Ensure your end users install the latest desktop app and register their device.
Once the TCP Service is defined, your end users will see it in their desktop app.
When the user clicks Connect, the Desktop App will launch the banyanproxy in TCP Mode, on the specified port (we recommend 3306 for MySQL).
The user can now use the MySQL Client (mysql) to access the Database by using their Login Certificate. IN this example we’ve set the port to 3306, and are connecting to the default database as the root user:
mysql -h 127.0.0.1 --P 3306 default -u root --ssl-mode=PREFERRED --ssl-cert="/Users/shivanshvij/Library/Application Support/banyanapp/login-cert.pem" --ssl-key="/Users/shivanshvij/Library/Application Support/banyanapp/login-key.pem"
The MySQL Database will validate the CSE-issued short-lived login certificate to allow database access.
Audit logs
You can grab granular logs of authorized accesses and unauthorized attempts. Instructions coming soon!